Infrastructure as Code: Do We Still Need IaC in the Age of AI Agents?
AI agents provision cloud resources through APIs, interpret observability data in real time, and respond to incidents without human intervention. Terraform plan, review, apply: is this cycle still fit for purpose when an agent can implement the same change in seconds?
The short answer: yes. More than ever.
Because anyone who turns agents loose on production infrastructure without solid guardrails is simply trading manual mistakes for automated ones—faster, and with a far bigger blast radius. Infrastructure as Code isn't becoming obsolete. It's becoming the governance layer that defines a safe operating envelope for autonomous agents. The key is a clear trust-level framework: how much autonomy is justifiable today, and which guardrails need to be in place to support it?
What is Infrastructure as Code, and why has it become the standard?
Infrastructure as Code means that infrastructure is described in code rather than configured manually. Tools like Terraform, Pulumi, CloudFormation, and Bicep let you define servers, networks, and databases declaratively, version them, and roll them out automatically.
Reproducibility and consistency
The biggest advantage of IaC is determinism. The same code produces the same result—whether in development or in production. That eliminates the classic "works on my machine" problem at the infrastructure level.
Auditability through versioning
Every infrastructure change is traceable in the Git history. Who changed what, when, and why? For regulated industries like finance and healthcare, that isn't optional—it's mandatory.
Scale and collaboration
Infrastructure as Code lets teams spin up hundreds of environments from a single template. Pull requests and code reviews turn infrastructure changes into a team sport, just like application code.
The case against IaC: AI agents can manage infrastructure directly
AI agents are getting more capable by the day. They interpret logs, analyze costs, flag security issues, and can create or change resources directly via cloud APIs. So why bother with the detour through declarative code?
Speed and responsiveness
An agent reacts in seconds. No plan-apply cycle, no waiting on CI/CD pipelines. When a service is under load, an agent can scale it immediately without anyone touching a Terraform file.
Cross-silo context
Where humans toggle between monitoring dashboards, cost explorers, and architecture documentation, an agent sees all of those data sources at once. That enables decisions that factor in multiple dimensions simultaneously.
Less complexity for end users
No state file management, no provider versions, no HCL syntax errors. AI agents could democratize infrastructure management and make cloud resources accessible to teams outside of DevOps.
Efficiency and cost savings
Agents meaningfully reduce manual ops work: fewer on-call incidents, faster incident resolution, less coordination overhead between teams. For middle management, that's a compelling lever for justifying automation investments to the C-suite.
Why we need Infrastructure as Code now more than ever: guardrails for AI agents
The strength of AI agents—their speed and autonomy—is also their biggest risk. And for many organizations, the more pressing question isn't whether to adopt AI agents, but whether their teams are already using them without any governance structure in place. This is exactly where Infrastructure as Code becomes an indispensable safety layer.
A declarative target state as contract
IaC defines what should exist. An agent can decide how and when to apply changes, but only within that defined envelope. The declarative target state becomes the contract between human and machine.
Policy-as-Code as a safety net
Tools like OPA/Rego, Sentinel, and Checkov define rules that every infrastructure change must satisfy. These policies are non-negotiable when an autonomous agent is making changes. They prevent an agent from accidentally exposing a database to the public internet or opening a security group too widely.
Blast radius control
A human working manually makes one mistake at a time—slowly enough to contain the damage. An agent without guardrails can delete a production database with a single API call. Infrastructure as Code enforces review gates and approval processes that cap the blast radius of every change.
Compliance and auditability
"The agent did it" won't satisfy any auditor. Regulated organizations need a versioned, traceable change history. IaC delivers exactly that—even when the change was initiated by an agent.
Deterministic reproducibility
Agent decisions are often non-deterministic. The same context can lead to different outcomes. For disaster recovery, that's untenable. Infrastructure as Code guarantees the same input produces the same result. That guarantee is not up for debate.
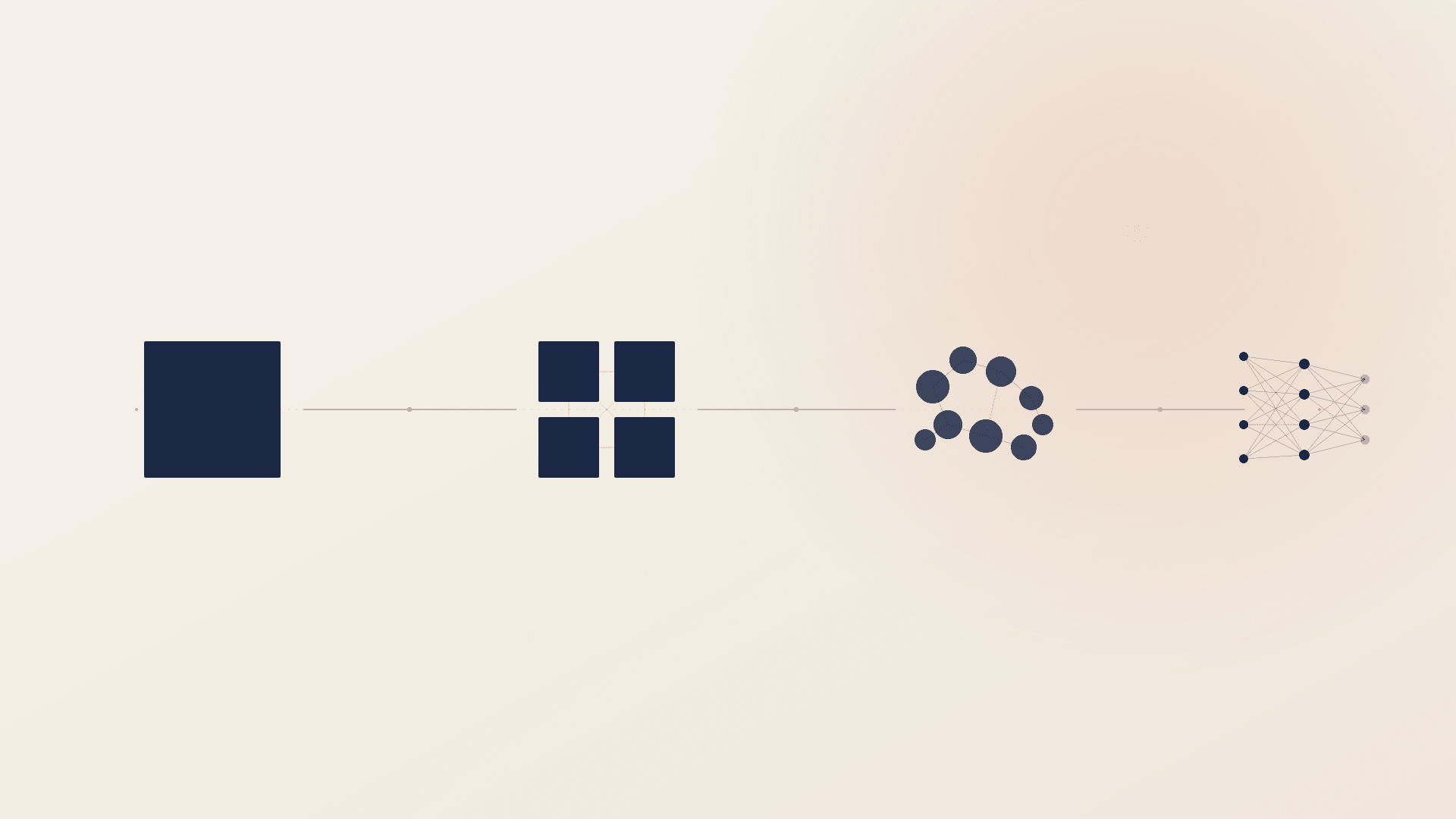
A question of trust: the trust-level framework for AI agents
How much autonomy should you grant AI agents in your infrastructure management? The answer isn't binary—it's a spectrum. Drawing on established autonomy frameworks like the SAE levels in autonomous driving, we can formulate a tiered trust-level model for infrastructure management as well.
The key point: trust is a risk-based decision. The right trust level isn't a technical question—it's an organizational one. It depends directly on your risk appetite, the criticality of the systems involved, and your regulatory obligations. Frameworks like NIS-2 and ISO 27001 set the boundaries here. NIS-2 requires demonstrable risk management for network and information systems; ISO 27001 calls for documented controls and continuous risk assessment. Anyone turning AI agents loose on infrastructure has to position their chosen trust level within that context—and be able to justify it on record.
Level 0: Read-only
The agent observes and reports. It summarizes monitoring data, flags anomalies, and informs the team. No write access to the infrastructure whatsoever.
Level 1: Suggest
The agent proposes changes—for instance, as an automatically generated pull request against a Terraform module. The decision and the execution remain with a human.
Level 2: Act with approval
The agent drafts a concrete change plan and executes it after human sign-off. Today, this is the most realistic entry point into agent-assisted DevOps.
Level 3: Act within boundaries
The agent acts autonomously, but only within clearly defined limits. Auto-scaling within configured min-max ranges, or self-healing based on predefined runbooks, are typical examples.
Level 4: Full autonomy
The agent manages the infrastructure entirely on its own. For production environments, this level is hardly defensible today—there are no established standards for reliability, explainability, or liability.
Most organizations are currently at Level 0 to 1. The realistic sweet spot for the next two to three years is Level 2 to 3.
Looking ahead: how AI agents will reshape infrastructure management
Infrastructure as Code isn't going away. But it is changing.
From writing to reviewing
DevOps engineers will write less IaC themselves and spend more time reviewing agent-generated proposals. The core competency shifts from syntactic knowledge toward architectural judgment and critical review.
Intent-based infrastructure
Instead of "spin up a t3.large EC2 instance," teams will say: "I need a service that can handle 1,000 requests per second." The agent picks the right implementation—within the guardrails that IaC and Policy-as-Code define.
Continuous reconciliation
Agents will monitor drift in real time and correct it autonomously. The declarative target state from the IaC code remains the authoritative reference.
Conclusion: Infrastructure as Code becomes the operating system for AI agents
The question isn't "Infrastructure as Code or AI agents?" They belong together. IaC provides the declarative framework, the auditability, and the deterministic reproducibility. AI agents bring speed, context awareness, and adaptability.
Infrastructure as Code isn't becoming redundant. It's becoming the foundation on which AI agents can operate safely and under control. Investing today in solid IaC practices, Policy-as-Code, and a well-designed trust-level framework creates the conditions for infrastructure management that keeps pace with agents—without giving up control.
The decisive question for your team isn't whether AI agents are coming. It's: what trust level are you prepared to grant, and which guardrails will you put in place to support it? How you determine the right trust level for your organization, and how you establish the necessary guardrails, depends on your individual risk profile. At Posedio, we help organizations build infrastructure management that stands up to this intersection of automation, governance, and regulation—future-proof by design.